Tag: command
Profanity: The Command Line Instant Messenger
Profanity is a text based instant messaging application which uses Command line Interface (CLI), which beats many GUI (Graphical User Interface) applications of a...
Apache OpenNLP: A Command Line Approach
Natural language processing (NLP) is a field of computer science, artificial intelligence and computational linguistics that explores the relationship between computers and natural languages....
Explore LaTeX and Syntax Highlighting with Scilab
This article, the last of a four-part series on Scilab, takes a look at LaTeX and syntax highlighting with Scilab. It is aimed at...
Linux Without Wires The Basics of Bluetooth
Bluetooth technology is used for short range (1 metre to 100 metres) communication. It is the most widespread wireless technology, and is divided into...
A Peek Into Open Source Verilog Simulator
Verilog, a hardware description language, is used to model electronic systems, and to design and verify digital circuitry at the register-transfer level of abstraction....
Carry Out Data Mining and Machine Learning with WEKA
WEKA is a collection of visualisaton tools and algorithms for data analysis and predictive modelling. It is very popular among users and developers as...
Jumpstart Linux Kernel Module Programming
Here's an introduction to the Linux kernel module, along with an explanation on how to write a simple pluggable module to the Linux kernel...
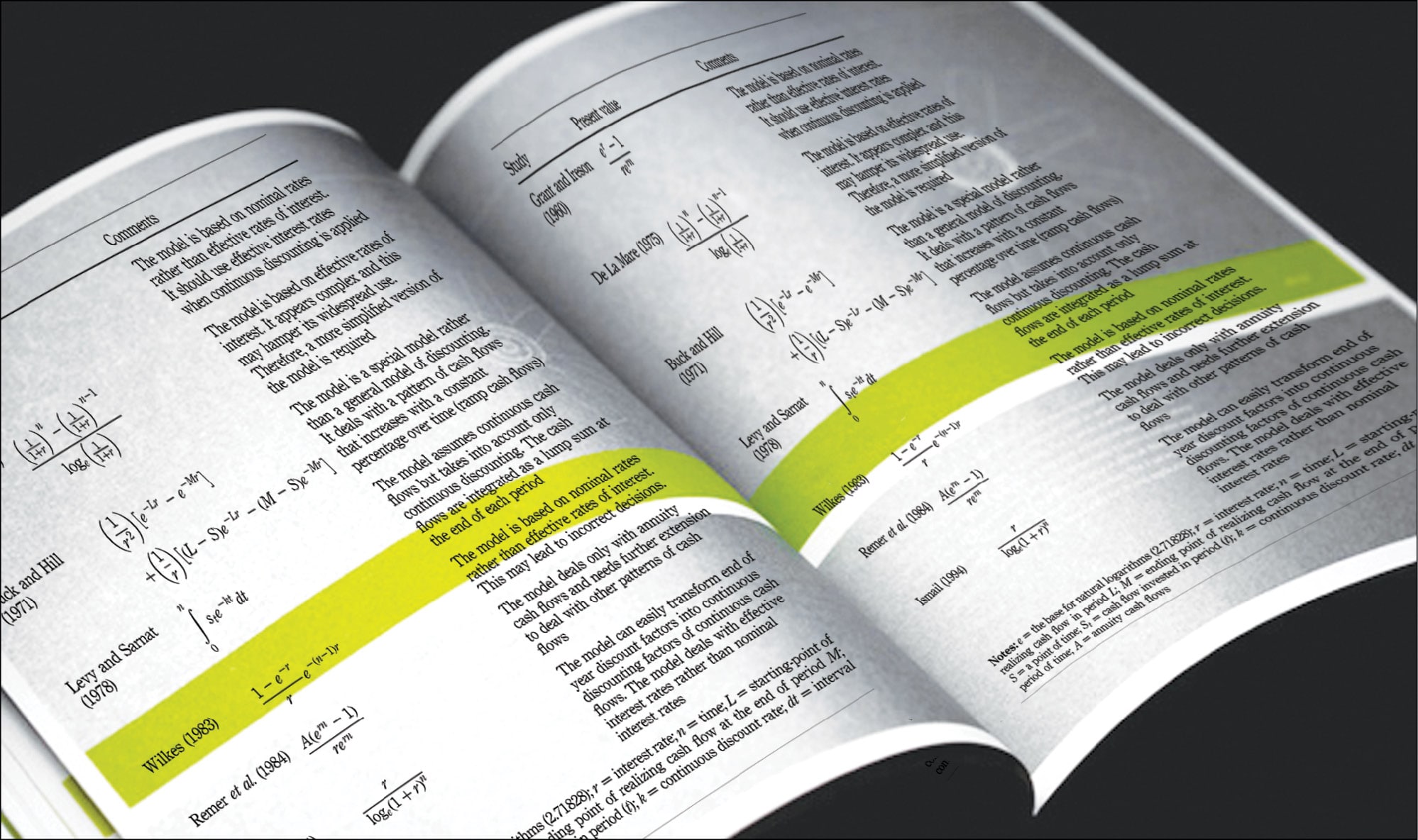
The CloudSim Framework: Modelling and Simulating the Cloud Environment
CloudSim provides a generalised and extensible simulation framework that enables seamless modelling and simulation of app performance. By using CloudSim, developers can focus on...
Secure Your Network with Firewall Builder
A firewall isolates a trusted, secure internal network from another network like the Internet, which is not regarded as either trusted or secure. Firewall...
Set Up a Certificate Authority in RHEL5
Security certificates are widely used for authentication. This article explores how to set up a Certificate Authority in RHEL5.
Security certificates are basically used for...