Infrastructure as a Service or IaaS is a popular cloud service today. With cyber threats on the rise, it’s important to use tools that ensure the security of these services as well as monitor them.
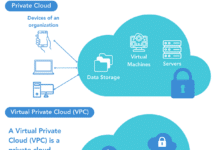
Infrastructure as a Service (IaaS) is a service model that enables on-demand resource provisioning for compute, storage and network with a pay-as-you-go model. Users are not required to bear upfront capital costs. They can specify the resources they need as IaaS consumers, and can provision the virtual resources. It is the IaaS producer’s responsibility to maintain the actual physical resources.
Security is one of the key pillars of a cloud infrastructure. The primary focus of security is on:
- Security information and event management systems
- Host intrusion detection systems
- Extended detection and response systems
- Anomalous behaviour prediction systems
How is IaaS made secure?
A number of key activities help make IaaS secure. Most cloud providers carry out these activities, which include:
- Periodic database scans
- Threat protection
- SQL injection
- Brute force
- Suspicious login
- Data exfiltration
- Send alerts
- Vulnerability assessment
- Audits
- Follow remediation steps
- Respond to hardware events
- Allow queries on running processes
- Network connection status (open/closed)
- Monitor system calls
- Firewall analysis
- Log analysis
- Network traffic monitoring
- Check on suspicious and anomalous behaviour
Emerging standards: The Open Cybersecurity Schema Framework
A number of standards and frameworks are emerging to cater to the security needs of IaaS services. The Open Cybersecurity Schema Framework is an open source, extensible framework that provides vendor-neutral core security schema. It’s an extensible framework — vendors and data owners can extend it to develop their own schemas for specific domains. This is helpful in building secure data pipelines as well as a common vocabulary for threat detection and resolution. The goal is to provide an open standard, which is adopted in any environment, application, or solution, while complementing existing security standards and processes.
Security in AWS (Amazon Web Services)
In the AWS cloud, there are a number of tools and services that can help with cloud security management. A few of them are listed below.
1. WAF
- Web Application Firewall (WAF) detects cyber attacks, such as DDoS or Distributed Denial of Service attacks in real-time, based on the rules configured
- Helps get real-time visibility into the attacks
- Can be linked to monitoring tools like CloudWatch
2. Advanced Shield
- Helps with anomaly detection
- Has 24/7 support
- Offers network flow monitoring
- Provides traffic (layer 7) monitoring
3. Security Lake
- Centralises and manages security data from the cloud, on-premises and custom sources into a common location for insights
4. Security Hub
- Provides a consolidated view of the security issues
- Helps to build custom responses and remediation actions
5. Macie
- Scans the S3 buckets for sensitive information (personally identifiable information, etc)
6. Inspector
- Performs a vulnerability analysis at scale for software vulnerabilities and network exposure
7. Guard Duty
- Uses machine learning techniques to identify suspicious user and resource behaviour
8. Detective
- Can analyse logs for security issues
9. Firewall Manager
- Enables centralised management of firewall rules across various accounts in AWS organisations
Monitoring IaaS
Monitoring, management and governance are key elements of IaaS cloud infrastructure. This includes, but is not limited to:
- Virtual server monitoring
- Virtual network monitoring
- Container monitoring (Docker/Kubernetes, etc)
- Database monitoring
- Cloud activity monitoring
The key characteristics of an IaaS cloud monitoring system are:
- Should be highly available to keep track of other systems and services
- Provide real-time notifications and alerts on outages and service degradation
- Immediately detect service outages and unauthorised activities
- Should be highly scalable to meet the demands of spikes in activity
- Be able to handle and process huge amounts of monitoring data
- Be able to collect standardised metrics using vendor-neutral standards
- Should support native and hybrid cloud services and applications
- Should allow end-to-end traceability
- Should have an intuitive UI for usability
- Should be able to integrate with visualisation tools
Prometheus, Icinga and Cacti are some of the most popular open source tools used for monitoring IaaS services.
IaaS security and monitoring is an emerging field, and cyber security is a niche skill. The nature (and scope) of cyber threats is on the rise. Organisations should follow the security-by-design approach, and make security and monitoring an intrinsic part of their develop-build-test-deploy activity. When properly architected and designed by including the security principles, organisations can build robust applications.