The previous article on customer identity access management (CIAM) published in the March 2019 issue of OSFY covered the basics, as well as the importance of an enterprise solution in a digital enterprise integration architecture. This article looks at the features of two CIAM solutions.
Customer identities are the core functionality expected of any digital transformation architecture; handling customer data without compromising size, security and flexibility to transform and exchange are the most important factors when preparing an integrated solution with CIAM frameworks.
Gigya
Gigya is based on the enterprise platform solution for CIAM featuring the customer-first approach to building a single view of each customer (designed for privacy and compliance). Gigya provides intelligent solutions for comprehensive security against DDoS and account takeover attacks. It is a flexible CIAM solution with visualisation reports, multi-factor authentication, and password management using the enterprise preference manager tool. It is preferred for enterprise solutions but is not suitable for cloud adoption.
When dealing in any industry context where there is identity and access management involved along with policies and roles for user access, the system of the record’s location may be influenced by a number of factors:
- Whether the data is sensitive enough to require a high grade of security and control
- The regulators’ rules
- Sovereignty of the information
- Suitability for cloud adoption/migration
- Visualisation support for customer data management
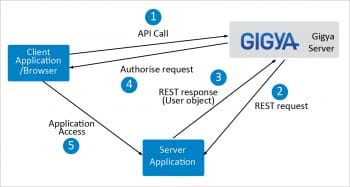
Gigya provides unified access management (UAM), including solutions for mobile identity management and privileged access management. The Gigya solution includes federated SSO with SAML, and social media identity registration and linking.
Gigya provides the account API, REST API, data store API and social network identification API as part of its SDK for developers. Detailed documentation and API references are available at developers.gigya.com.
Gigya provides a data store that is a flexible, fully indexed dynamic schema based store for handling customer identification details. The data objects are in JSON format and are limited to a maximum of 512k. Querying the data store is possible using a SQL-like REST API called ds.search and the data model is returned as a JSON result set. Details on the usage of the data model, the data store and its API are available at developers.gigya.com/display/GD/Data+Store.
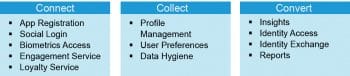
The features offered by Gigya with respect to user data handling are categorised into Connect, Collect and Convert.
The advantages of choosing Gigya for your integration architecture are:
- Visualisation dashboard and reports
- Dynamic system or record schema
- Account management
The disadvantage of choosing Gigya for your integration architecture is that it is an out-of-the-box SaaS offering. Hence, it has no ready-made feature for SaaS integration, and users have to do manual integration.
Janrain
Janrain is one of the pioneering CIAM solutions with a unique combination of customer profile management and marketing insights. It is the first CIAM solution that comes with universal integration of CIAM event data with security information and event management (SIEM) systems like IBM QRadar. Data breaches and fraudulent transactions are due to compromised user accounts. Janrain is a complete solution for handling and avoiding such malicious activities. It is now part of the Akamai cloud delivery platform.
When dealing with CIAM integration in an industry context, profile management may be influenced by a number of factors:
- The flexibility to adopt at runtime
- User notification
- Customisible and extensible
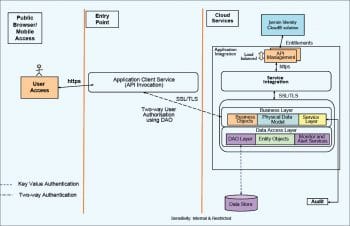
For effective profile management, one can choose the Janrain Identity Cloud solution. One of the key unique features of a Janrain solution is that it can prepare user notifications on malicious attacks and compromised user accounts using an integrated CIAM solution.
The Janrain solutions architecture is based on the following key principles:
- Flexibility to integrate a digital transformation solution
- Data governance
- Identity security
The advantages of choosing Janrain for your integration architecture are:
- Customer profile management
- REST API support
- Marketing insights
The disadvantage of choosing Janrain for your integration architecture is that dynamic schema is not supported.
Future articles in this series will cover more CIAM solutions along with their features, integration patterns, advantages and disadvantages – particularly their integration with digital transformation architecture.














































































