Data security vulnerabilities can result in tremendous losses, damage to reputation, and even national security threats. In this article, we discuss the top open source tools that will help systems administrators to enhance network security. A few of these are time tested, while others are new entrants trying to make a mark.
The past year has been a turbulent one for those in the cyber security domain, with events ranging from large scale malware attacks to the improper use of voter data in political campaigns hogging the headlines. Privacy concerns have risen to the fore with the European Union coming down heavily on the unregulated and possibly unethical use of personal data with the introduction of the GDPR (General Data Protection Regulation). There have been cyber attacks galore, without major public incident, save for the ‘small’ issue of millions of computers attacked by WannaCry and its successor, Petya.
Of course, the major leaks in the past year included parts of the CIA and NSA toolkits, and strategies to employ vulnerability brokers – overall, the year exposed the dark and murky secrets employed by the top intelligence agencies in their all-out effort to gain an edge in counter-terrorism efforts.
On the corporate front, fresh from the Cambridge Analytica scandal, Facebook announced a horde of changes targeted at alleviating user concerns regarding privacy. Amid all the furore over data, privacy and ethics, numerous tools have been introduced to address cyber security concerns. In this article, we delve into the list of the top open source tools for network security and a few new entrants.
The direction of growth
The past few years have seen the world plagued by large scale password leaks, DDoS attacks on widely used code hosting websites and, most recently, the accidental exposure of plaintext passwords by leading social networks. The recent focus on ethics and policy regarding data usage has seen much debate over the very definition of ethics. Overall, the industry seems to be growing more responsive to user concerns as most companies are falling in line with the GDPR, which has been ratified within the European Union. While the intrusion detection and security markets are largely catered to by the likes of proprietary offerings like McAfee, Symantec and Juniper, various open source variants are also being deployed within a large number of corporates. Intrusion prevention and detection has been the major focus in the launching of such tools. Let’s look at what’s on offer under the following two categories–the good old legends of network security and the newcomers finding a foothold in the industry.
The stalwarts
NMAP: Possibly the most popular port scanning tool of all time, NMAP has been going strong with an active community to back its development and adoption across the world. It is used to scan and map the network and various ports, and is backed by a powerful set of NSE scripts that can be employed to test and detect misconfigurations and security issues on the network. NMAP also sports its own version of Netcat, which is touted to be more powerful than the original. It has seen the addition of OS fingerprinting features and the expansion of the NSE scripts, among other performance improvements.


The Metasploit Framework: Impossible to miss out on, the Metasploit Framework focuses on defence from the view of the attacker. It offers a toolkit tailored to aid the security team in aggressively testing its own system for vulnerabilities —to perform security audits, and generate reports and assessments. The software comprises an arsenal of tools with contributions by experienced penetration testers in order to arm the defenders of a system against the strategies adopted by attackers.
Kali Linux: Most tried and tested approaches to penetration testing use the legendary Kali Linux system. Kali offers an entire operating system dedicated to the single task of emulating an infiltrator within the network. It is supported by a robust development environment with thousands of packages available for use. Recent releases have focused on addressing the much-hyped Spectre and Meltdown vulnerabilities and now support hardware-level encryption of sorts.
Bro IDS: Marketed as the software that has successfully brought together research and implementation, Bro is an intrusion detection system that has been developed at Berkeley and the National Centre for Supercomputing Applications at Urbana-Champaign, Illinois, USA. Focusing on network security and monitoring, it provides a comprehensive platform for network traffic analysis.

Wireshark: Running on Windows, OS X, and UNIX, Wireshark is one of the most effective network packet analysers. It offers a variety of capturing and analysing options, along with a well-designed interface to visualise and view the contents and details of the captured data. Alternatives that focus on the command line execution include Tshark and Tcpdump.
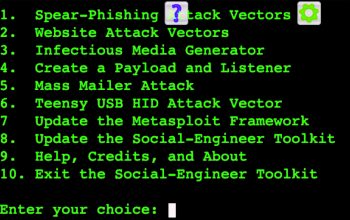
Social Engineering Toolkit (SET): One of the more fun tools to play around with, the SET presents, quite literally, a menu of options that can be leveraged to exploit the human factors that impact the system. It focuses on phishing, malware delivered via infected PDF files and other social engineering practices that can be used to bypass the security rules within a system. Using SET, security teams can design and deploy internal attacks on members of the organisation in order to test the security awareness and resilience of the network.
The new entrants
We now shift our focus to a few noteworthy tools that caught our attention based on their popularity in the open source community.

WiPi Hunter: This is designed to detect illegal wireless network activities performed by special software and hardware, and comprises various modules involving fake access points for monitoring and analysis, detection of attacks using KARMA, apart from calculating a wireless security score.

WHID or WiFi-HID Injector: Since the initial appearance of HID attacks, many tools and devices to guard against them have been released. However, offensive security researchers were always seeking cheap and dedicated hardware that could be controlled remotely and that’s how the WHID Injector was born. It has been designed using an Atmega 32u4 and an ESP-12, which means it can be easily controlled over the Wi-Fi network and potentially bypass air-gapped environments.

Leviathan Framework: Leviathan is a mass-audit toolkit comprising various features including SQL injection, custom exploits, brute force attacks and wide range service discovery. It offers the flexibility of using tools like dsss, massscan and ncrack, or a combination of these. The goal is to audit as many systems as possible within a wide IP range.
LuLu: As its website states, the world has turned into a Web of connected devices. And often, the root cause of these problems is the very connection that initiated the Web. LuLu presents a fresh perspective; it is a firewall that aims to block all outgoing connections unless explicitly approved by the user.














































































[…] While the intrusion detection and security markets are largely catered to by the likes of proprietar… […]
Fortunately for small businesses, they have a safety net that can help them deal with such challenges. That safety net is managed IT services which especially enable small businesses to scale when a growth spike comes around and also enable them to free their IT personnel for more strategic and productive uses over time.