Firewalls have gained importance due to the increasing number of malicious attacks on networks and computers. Shorewall, a powerful offering from the Linux world, is primarily used to protect networks, as its strength lies in working with zones.
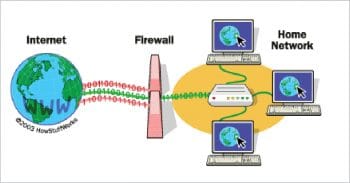
A firewall provides an additional layer of defence, insulating the internal systems from external networks. The primary task of a firewall is to examine all the traffic routed between two or more networks according to certain defined rules and policies. Only if the terms of the rules and policies are complied with, is traffic routed between the networks; otherwise, all the packets are dropped. There are two access denial methodologies followed by firewalls, i.e., allow traffic or deny/restrict traffic. A firewall may allow all traffic through because it meets specified criteria, or it may deny all the traffic unless it meets certain criteria. The type of criteria used to determine whether the traffic is allowed through depends on how the user configures the firewall settings. Firewalls can also use complex rules as the basis to analyse the application data, prior to determining if the traffic should be allowed or rejected.
A firewall plays a crucial role in preventing unauthorised access to devices or networks. Its function is to carefully inspect the data entering or exiting the device, based on user configurations and deny access to data that comes from a suspicious network. It can also be used to log all attempts to enter the private network and trigger alerts when any sort of unauthorised entry is attempted.
Types of firewalls
There are primarily two main types of firewalls – hardware firewalls and software firewalls.
Hardware firewalls: These are systems that are independent of the computers that they protect. They filter information from the Internet as it passes into a computer. Most of the Wi-Fi or Internet routers have inbuilt firewalls for packet filtering. In general terms, hardware firewalls work by examining the data that flows in from the Internet and verify whether that information is safe. Simple firewalls, known as packet filters, examine the data itself for information such as its location and its source. Then the information the firewall gathers is compared to a set list of permissions in order to determine whether the information should be dropped or allowed through.
Hardware firewalls have become more advanced these days, and are capable of analysing data on various parameters, including the time of entry into a network, etc.
Software firewalls: For individual home users, the most popular are software firewalls. These can be installed like any other computer software, allowing users to control the functions and choose protection policies. A software firewall protects the computer from outside attempts to gain control over the system and also contends with a wide variety of Trojans, rootkits, viruses, malicious software, worms and even ransomware. Software firewalls are equipped with privacy controls, Web filtering capabilities and many other features. They run in the background and use limited resources.
There are many differences between hardware and software firewalls, but for the best protection of computers and networks, most administrators use both.
Types of software firewalls
The following are the types of software firewalls:
- Packet filtering firewalls
- Circuit level gateways
- Application level gateways
- Stateful multi-layer inspection firewalls
Packet filtering firewalls: These apply a set of rules, and examine each packet to determine whether to forward or drop a packet towards a particular destination. The firewall is configured to filter the packets going in both directions – inbound and outbound. Packet filtering firewalls permit or deny network traffic on the basis of the following information:
- Source IP address and destination IP address
- Protocols like UDP and TCP
- Source and destination ports
- Direction – inbound or outbound
- A physical interface with packet flow
Circuit level gateways: Circuit level gateways work at the session layer of the OSI or Open Systems Interconnection model. They monitor the TCP handshake between the packets to determine if a requested session is legitimate and whether the information passed through a circuit level gateway, to the Internet, appears to have come from the circuit level gateway. So, for instance, there is no way for a remote computer or a host to determine the internal private IP addresses of the organisation. This technique is termed as network address translation, whereby the private IP addresses originating from the different clients inside the network are all mapped to the public IP address available via ISP and sent to the outside world.
Application level gateway firewalls: These decide whether to drop a packet or send it based on the information about the application. This is done by setting up proxies on a single firewall for different applications. Both the client and server connect to the proxies instead of connecting directly to each other. So, any sort of suspicious data is dropped by proxies and complex protocols like H.323, SIP, etc, can also be handled. Application level firewalls can look in to individual sessions and decide to drop a packet based on information in the application protocol headers or in the application payload.
Stateful multi-layer inspection firewalls: Stateful multi-layer inspection firewalls combine the aspects of all the above types of firewalls. They filter packets at the network layer, transport layer and application layer, allowing the packets to pass through if these layers pass all of them, individually. Some of them allow direct connection between the client and the server, as they rely on algorithms to recognise and process application layer data instead of relying on application specific proxies. These offer more security, performance and transparency to end users.
Linux based firewalls
A Linux based firewall is controlled by a program called iptables, which handles packet filtering. It is an administration program built inside the Linux operating system. It works at the transport layer and protects the system by making routing decisions after filtering the packets, based on information in the IP packet header. Iptables requires root based administrative privileges to operate and can only be executed by the root user. It is used to set up, maintain and inspect packet filters in the Linux kernel. Every table contains user-defined chains, and each chain consists of lists of rules applied to incoming packets. Every rule specifies what to do with a packet that follows the rules. The rules are related to accepting or dropping the packet entering the private network from the outside world.
In order to select a firewall for Linux, there are various concerns with regard to installation, configuration, documentation, features, operation and even support. There are a large number of firewalls available, like IPCop, Shorewall, Monowall, etc. Shorewall is regarded as one of the most powerful firewalls in Linux.
Introducing Shorewall
Linux security is based on the Netfilter system, which is a powerful framework provided by the Linux kernel to perform all types of network operations like packet filtering, NAT, port translation and packet blocking from external sources. Netfilter is implemented via user-space applications and iptables. The latter is powerful, yet complex to work with. So, to make Linux systems more secure, the Shorewall firewall has emerged as a good choice.
Shorewall is a gateway/firewall configuration tool for Linux and is regarded as a high-level tool for configuring Netfilter. All the firewall requirements are entered by users in configuration files. These configuration files are read by Shorewall, and with the support of iptables, iptables-restore, ip and tc utilities, the firewall configures Netfilter in the Linux kernel. Shorewall can be used as a dedicated firewall system or a multi-functional gateway/router/server in the Linux system. Shorewall is a Perl based wrapper for IP tables.
The main objective behind the development of the Shorewall firewall was to create an abstraction in the configuration of the firewall of a higher level, as compared to standard iptables. The advantage of this mechanism is that it divides the interfaces into zones with different levels of access so that the user can operate on a group of computers, instead of addresses, connected to the interface. In the Shorewall system, users can deploy policies for the zone in an easy and comprehensive manner.
Shorewall is not a daemon running in the background but is better known as a shell script, which converts configuration files into the iptables commands.
Shorewall firewall configuration files
The following files operate the overall Shorewall firewall:
- /etc/shorewall/shorewall.conf – This configures global firewall parameters.
- /etc/Shorewall/params — This is the file that sets shell variables to expand in other files. It is processed by /bin/sh or by the shell specified via SHOREWALL_SHELL in the
- /etc/shorewall/Shorewall.conf file.
- /etc/shorewall/zones – This partitions the firewall’s view of the world into zones.
- /etc/shorewall/policy – This establishes the firewall’s high-level policy.
- /etc/shorewall/initdone – This is an optional Perl script, which is executed by the Shorewall rules compiler after finalising installation.
- /etc/shorewall/interfaces – This explains the interfaces on the firewall system.
- /etc/shorewall/hosts – This file helps users to define zones in terms of individual hosts and sub-networks.
- /etc/shorewall/masq – This file directs the firewall when to use many-to-one (Dynamic) NAT and Source NAT (SNAT).
- /etc/shorewall/mangle – This file contains rules for packet marking, TTL, proxies, etc.
- /etc/shorewall/rules – This file lists exceptional rules to overall policies in /etc/shorewall/policy.
- /etc/shorewall/nat – This defines one-to-one NAT rules.
- /etc/shorewall/proxyarp – This defines rules with regard to proxy ARP.
- /etc/shorewall/tcrules – This is used for traffic controlling/shaping and policy routing.
- /etc/shorewall/tunnels – This defines VPN based rules.
- /etc/shorewall/blrules — This is for a set of machines that are blacklisted.
- /etc/shorewall/init – This is for the commands to be executed at the start of Shorewall.
- /etc/shorewall/start – This is for commands executed after the start of Shorewall.
- /etc/shorewall/stop – This is for commands executed when Shorewall is stopped.
- /etc/shorewall/accouting – This is for IP traffic accounting rules.
- /etc/shorewall/providers – This is for alternate routing tables.
- /etc/shorewall/vardir – This determines the directory that will maintain the state of Shorewall.
Features of Shorewall
- Accounting: This appropriately counts the packets and bytes, using categories and rules specified by network administrators. It is a powerful tool that provides all sorts of information about inbound and outbound traffic.
- Supports many types of router/firewall applications: Shorewall is highly efficient in customising all the preferences of users via configuration files, and there are no limitations in network interfaces. It allows administrators to partition the network into zones and provides full administrative control over connections, permitted by every pair of zones.
- Tunnelling: Shorewall is efficient in creating tunnels for VPNs, like IPSec, PPTP, GRE, IPIP, OpenVPN, IPv6-over-IPv4, IPv4-over-IPv4 and others.
- Centralised administration: It can be monitored and administered via any network-connected system. It supports Windows and even Mac OS X.
- Support for address/routing management: It is equipped with tons of features which enable masquerading, port forwarding, one-to-one NAT, proxy ARP, NETMAP, multiple ISP support, etc.
- Support for virtualisation: Shorewall can efficiently work with a range of virtualisation software like KVM, XEN, Linux-VServer, VirtualBox, LXC and even Docker (for which support was recently added).
- Other features: Shorewall provides many other features like traffic accounting, IPv6, MAC verification, lots of RPM/Debian packages, and even blacklisting of individual IP addresses or subnets.
How Shorewall works
Shorewall works through configuration files located in /etc/shorewall as mentioned earlier.
In order to work effectively, the following files are used.
1. Interfaces: These give detailed information of the physical interface being used for filtering the inbound and outbound traffic.
2. Policy: This defines the policies for connections between zones.
3. Rules: These define the connection establishment via exceptions to the main policy file.
4. Zones: All network zones are defined here.
Shorewall processes run in the background and are able to handle multiple IPs at a single point of time.
Shorewall packages
The following are the six main packages available as part of the Shorewall firewall.
• Shorewall-Core: This is the core package to install Shorewall, Shorewall6, Shorewall-lite or Shorewall6-lite.
• Shorewall-Comprehensive: This package consists of everything needed to create the IPv4 firewall.
• Shorewall6-Comprehensive: This package consists of everything needed to create the IPv6 firewall.
• Shorewall-lite: This is a lightweight Shorewall version to run firewall scripts generated via the system that is already running Shorewall.
• Shorewall6-lite: This is a lightweight Shorewall6 version to run firewall scripts generated via a system already running Shorewall6.
• Shorewall-init: This is used to place the firewall in safe mode before running up the network interface.














































































Thank Dr Nayyar, I wasn’t aware of Shorewall firewalls. I’m going to have my development team look into this.