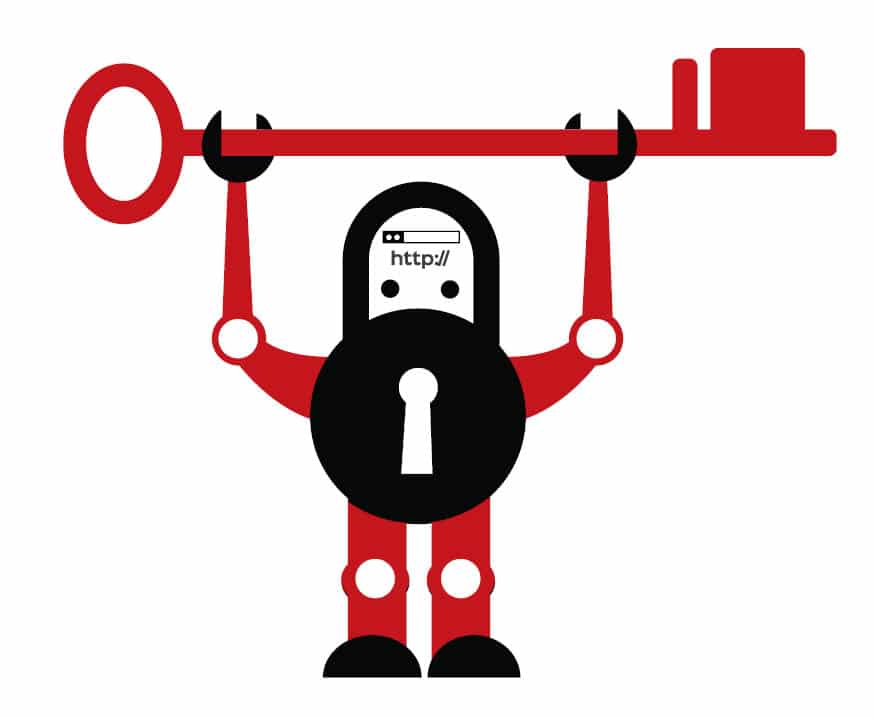
Even though we think we have secured our browsing by using conventional means, are we really secure from targeted advertising? Is our privacy secured when we browse the World Wide Web? Learn how we can secure our browsing and protect ourselves from browser fingerprinting.
Sign out, clear the cookies, and switch over to the private browsing mode — this is the privacy mantra of most Internet users. If you too fall into this category, then you better be aware that you’re being tracked. User accounts and cookies have become archaic when it comes to tracking. You might have noticed personalised ads which are related to your previous search queries, which seem to match your tastes accurately. This happens even when you are not logged in and have no cookies retained. This is made possible by a new tracking technique called browser fingerprinting, according to the Electronic Frontier Foundation (EFF).
The EFF is a non-profit organisation founded in 1990, aimed at protecting user privacy and freedom of expression in the digital era. It still fights this battle by conducting campaigns, doing research, and developing security and privacy tools. This is a valuable effort considering the fact that user tracking and immoral use of private information by websites have increased recently. You can learn more about EFF at eff.org.
Thanks to EFF and some software projects, we now have a bunch of free software tools to protect our privacy while browsing the Web. Let’s first learn what browser fingerprinting is and find out the EFF tools that present us with the solution.
Note: This article addresses trackers only. Blocking trackers can help you prevent things like personalised ads. But to be truly anonymous, you have to use anonymity networks like Tor, which is a topic beyond the scope of this article. Visit torproject.org for more details, and use it only for legal purposes.
Browser fingerprinting
Browser fingerprinting is a technique that can be employed by websites to track your activities even when you are not signed in and are browsing in private mode. But how does it work?
Well, it’s obvious that websites can track and record your activities while you are logged in since they clearly know who you are (at least what your user name is). Even if you are not logged in, they can still drop a cookie in your browser and associate any activity from the same browser with you, which is enough to serve you personalised ads.
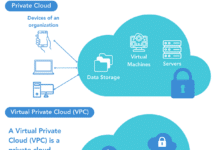
That’s why we switch over to the private mode, whereby we expect to be immune to the tracking mechanism just because we are not signed in and the browser doesn’t retain any cookies from our previous session. The site may still be able to obtain our IP address, but we feel it is of least importance when it comes to identifying us, since the IP address changes each time we connect to the Internet (unless we have a static IP connection).
But this assumption is false. Websites can still track you even though you are not willing to sign in or retain cookies. What they use to identify you is the fingerprint of the browser you use. Unlike a serial number, this is not something imposed on the browser by the developer. Instead, it is calculated by the websites based on the configuration and settings of the browser. They even consider the extensions that you use.
To put it simply, consider the example of identifying a vehicle. The most straightforward and accurate way would be to use the registration number (exclude spoofs). But in most cases, we simply say something like, “…a red SUV with an eagle sticker on the hood, tops removed, one mirror slightly broken.” This would be more than enough since such a combination will be unique in a particular city.
Browsers can also be identified like this. The parameters start from basic configurations and the operating system to some unimaginable ones, such as:
- Extensions used
- Plugins and file formats supported
- Screen resolution and colour depth
- Language and time zone
- Touchscreen support
Quoting panopticlick.eff.org, “Browser fingerprinting is a method of tracking Web browsers by the configuration and settings information they make visible to websites, rather than traditional tracking methods such as IP addresses and unique cookies.”
How to test your browser and what to do next
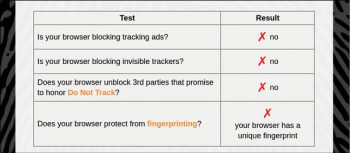
We’ve seen how a website can track our browser using browser fingerprinting. Now let’s figure out how susceptible our browser is. To check this, simply visit panopticlick.eff.org, which is the result of an important research undertaken by EFF.
You can see a TEST ME button on the home page itself. Click on that, and your browser gets tested. It takes a while, and once complete, you are presented with a quick report showing how your browser is susceptible to different aspects of tracking. You can get a detailed report, and install the privacy extension Privacy Badger from the same page.
Blocking trackers with Privacy Badger
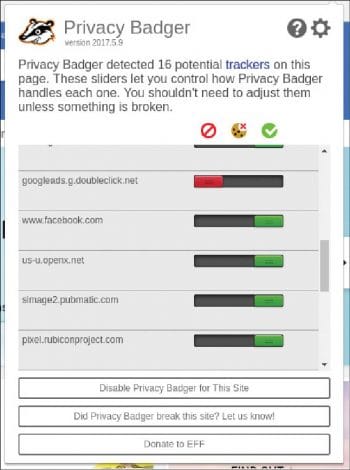
There are hidden trackers embedded in many websites in the form of scripts and cookies. They are used to track you, i.e., to create a record of the pages you visit, things that you like and things you don’t. These details are usually used to serve personalised ads, and sometimes are sold to a third party for business purposes. The EFF Privacy Badger is a useful extension that blocks such trackers. Visit eff.org/privacybadger to install this add-on in your browser.
When Privacy Badger realises that the ads in a page are tracking you, it simply blocks the trackers from loading more content. To borrow the words used by EFF, “…to the advertiser, it’s like you suddenly disappeared.”
When you install Privacy Badger and visit a website with trackers, it will display a list of these with sliders if you click on its icon in the browser toolbar. The slider will probably be green the first time, which means that the tracker is still not tracking you and hence is allowed. As you continue browsing, the slider might turn yellow and then red, indicating Privacy Badger’s opinion on them, and the blocking level.
You can say that Privacy Badger acts like an ad blocker and in fact, it is based on the code of AdBlockPlus. Still, it’s a bit different. Its aim is not to block every ad, but to block every tracking element. This is important since not all ads are tracking you and we don’t want to block some innocent ads that help the creators run their websites. Moreover, tracking elements don’t always come as part of ads. Privacy Badger targets trackers regardless of their relationship with ads, which is a behaviour that requires additional configuration in regular ad blockers.
The Do Not Track header
Do Not Track (DNT) is a proposed HTTP header field that tells a website that you wouldn’t like to be tracked. Firefox’s Private Mode has this feature enabled, by default, whereas Chromium does not. You can enable this feature even in the regular mode by visiting the privacy and security sections of your browser’s settings page, if it supports it.
To know more and to check your browser, visit allaboutdnt.com (not from EFF).
HTTPS Everywhere
We all know that HTTPS is a mechanism that helps us encrypt our communication with Web servers, making it impossible for eavesdroppers to tap or manipulate our data. The URLs of HTTPS-enabled pages start with https:// instead of http://.
However, not all websites use HTTPS. And among the ones that are HTTPS-enabled, not all enforce it. This means you might be at risk even if you are visiting an HTTPS-enabled website, but have forgotten to ensure that your address bar shows https:// instead of http://. Another unfair practice is websites loading some third-party or additional resources over HTTP, even if the whole page’s address starts with https:// (some browsers display a broken lock icon to indicate this).
The HTTPS Everywhere extension helps you in such situations by rewriting the HTTP requests from your browser with HTTPS, if the servers support it. Of course, it can’t make a website HTTPS-enabled if the server doesn’t have an SSL/TLS certificate installed or it intentionally disables HTTPS for certain pages. Then what is the use of such an extension, you might ask. But recall the fact that not all HTTPS-enabled sites default to it, and not all secure pages are 100 per cent secure since they load non-HTTPS elements also. This is where HTTPS Everywhere can be of some help and it really matters.
You can download this extension from eff.org/https-everywhere. It is worth noting that the Tor Project has also contributed to it.
What about the sites that don’t support HTTPS yet? Tell the webmasters how important HTTPS is, and how it can improve their reputation. Webmasters can get Let’s Encrypt SSL/TLS certificates for free, just by installing the EFF tool Certbot. If you are a webmaster who hasn’t got HTTPS yet, take action quickly!