Let’s have a look at the premier, free, open source, network intrusion and detection system called Snort. It is an amazing tool that lives up to its billing. This tutorial walks you through the basics of Snort.
Snort is a very popular open source network intrusion detection system (IDS). It can be considered a packet sniffer and it helps in monitoring network traffic in real-time. In other words, it scrutinises each and every packet to see if there are any dangerous payloads. In addition, Snort can also be used to perform protocol analysis, content searching and matching. And it can be used to detect various types of attacks such as port scans, buffer overflows, etc. It is available on Windows, Linux, various UNIX as well as all major BSD operating systems. Snort doesn’t require that you recompile your kernel or add any software or hardware to your existing distribution, but it does require that you have root privileges. It is intended to be used in the most classic sense of a network IDS. All it does is examine network traffic against a set of rules, and then alerts the systems administrators about suspicious network activity so that they may take appropriate action.
One can configure Snort in the following three different modes:
a. Sniffer mode
b. Packet logger mode
c. Network intrusion detection mode
In the sniffer mode of operation, Snort will read network packets and just display them on the console. In packet logger mode, it will be able to log the packets to the disk. In network intrusion detection mode, Snort will monitor the network traffic and analyse it based on the rules defined by the user. It will then be able to take a specific action based on the outcome. Please note that Snort has an inbuilt real-time alerting capability.
As expected, network IDS are placed at certain points within the network so that the traffic to and from all devices on the network can be monitored. Once an attack or an abnormal situation is identified, an alert can be triggered to the systems administrator to take corrective actions, as needed.
How to install and run Snort
Let us first understand how one can install Snort.
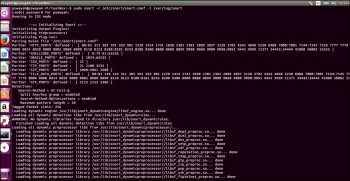
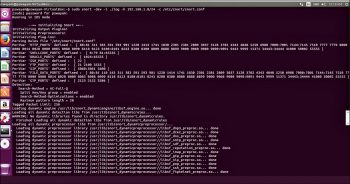
As a first step, execute the following command on your Linux terminal:
pswayam@pswayam-VirtualBox:~$ sudo apt-get install snort
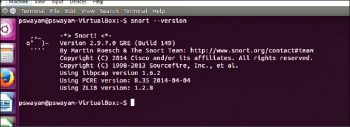
Once the installation is complete, you can check how successful the installation has been by using the following command:
pswayam@pswayam-VirtualBox:~$ snort –version
Snort comes with a very detailed man page and readers should go through it for a thorough understanding of this IDS.
A few more programs are needed if you want to run Snort. These are:
- Apache2 for the Web server
- MySQL-server for the database
- PHP5 for the server-based script
- PHP5-MySQL
- PHP5-gd for graphics handling
- PEAR (PHP Extension and Application Repository)
And we can use apt-get to install all the above programs as shown by the following commands:
pswayam@pswayam-VirtualBox:~$ apt-get install apache2 pswayam@pswayam-VirtualBox:~$ apt-get install mysql-server pswayam@pswayam-VirtualBox:~$ apt-get install php5 pswayam@pswayam-VirtualBox:~$ apt-get install php5-mysql pswayam@pswayam-VirtualBox:~$ apt-get install php5-gd pswayam@pswayam-VirtualBox:~$ apt-get install php-pear
As a next step, we need to create a set of directories required to successfully run Snort. One can use the following commands to create these files:
pswayam@pswayam-VirtualBox:~$ mkdir /etc/snort pswayam@pswayam-VirtualBox:~$ mkdir /etc/snort/rules pswayam@pswayam-VirtualBox:~$ mkdir /var/log/snort
The snort.conf file controls everything about what Snort watches, how it defends itself from attack, what rules it uses to find malicious traffic, and even how it watches for potentially dangerous traffic that isn’t defined by a signature. A very good understanding of what is in this file and how it can be configured is pretty essential for successful deployment of Snort as an IDS. By default, this configuration file is located @ /etc/snort. If the configuration is located somewhere else, then you need to specify a –c switch along with the file’s location.
Alerts are placed in the Alert file in your logging directory (/var/log/snort by default, or the directory you specify with the -l switch). Snort exits with an error if the configuration file or its logging directory does not exist. You can specify what type of alert you want (full, fast, none, or UNIX sockets) by supplying the -A command-line switch. You need to use the -A switch if you do not use the -c switch, or Snort will not enter alert mode. Additionally, if you use just the -c switch, Snort will use the full alert mode by default. The snort.conf file is used to store all the configuration information for a Snort process running in IDS mode. The majority of the snort.conf file’s content is commented-out instructions on how to use the file. Some of the popular configurable items of this snort.conf file are listed in Table 1.
Table 1
| Variable | Description |
| HOME_NET | Specifies the IP address of the system that you are protecting. So when you use Snort, you will need to change this parameter to your actual home network IP address range and do not leave this to the default value of ‘any’. |
| ORACLE_PORTS | Used to specify the port that Oracle is listening on. |
| RULE_PATH | Points to the location of the rule sets in your file system. Typically, rules are stored in /etc/snort/rules. So please make sure to use the full path name or whatever the right location is on your system. |
Please note here that to get Snort ready to run, one needs to change the default configuration settings to match your local environment and operational preferences. Also, if you want to change the settings of the default configuration file, you need to have root privileges.
It is very common to see include items in Snort configuration files. These are commands that instruct Snort to include the information in files located in Snort’s sensor’s file system. Typically, these files contain configuration related information and also the files that contain rules which Snort can use to catch bad behaviour. As expected, the actual rules themselves are not entered directly into the configuration file to simplify management.
One can set an alert in the rules files with the following structure:
<Rule Actions> <Protocol> <Source IP Address> <Source Port> <Direction Operator> <Destination IP Address> <Destination port > (rule options)
Let us take a quick look at the rule structure with an example of each:
| Structure | Example |
| Rule action | alert |
| Protocol | ICMP |
| Source IP address | any |
| Source port | any |
| Direction operator | -> |
| Destination IP address | any |
| Destination port | any |
| Rule options | (msg:”ICMP Packet”; sid:477; rev:3;) |
It is important to understand here that a few lines are added for each alert and these lines carry the following information:
a. IP address of the source
b. IP address of the destination
c. Packet type and useful header information
In order to execute Snort, one can use the following command:
pswayam@pswayam-VirtualBox:~$ snort -c /etc/snort/snort.conf -l /var/log/snort/
Now, a file called Alert will get created in the /var/log/snort directory. This file contains the alerts generated while Snort was running. Snort alerts are classified according to their type. A Snort rule specifies a priority for an alert as well. This lets you filter out low priority alerts to concentrate on the most worrisome. One can also run Snort as a daemon process by using the –D option as shown in the following command:
pswayam@pswayam-VirtualBox:~$ snort –D -c /etc/snort/snort.conf -l /var/log/snort/
Note that if you want to be able to restart Snort by sending the SIGHUP signal to the daemon, you will need to use the full path to the Snort binary, when you start it.
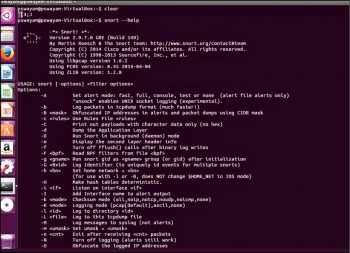
You can type snort –help to get a clearer understanding of the various options that are available with Snort.
How to use Snort
Let us now understand how to use Snort in various modes. As mentioned earlier, Snort can be configured in three modes – Sniffer mode, packet logger mode and network intrusion detection mode.
In Sniffer mode, Snort will be able to print TCP/IP packet headers to the screen. This can be done by using the following command:
pswayam@pswayam-VirtualBox:~$ snort –v
If you want Snort to display packet data as well as the headers, you need to add the –d option as shown below:
pswayam@pswayam-VirtualBox:~$ snort –vd
In some cases, we may even be interested in a more descriptive display and for this, we need to use the –e option.
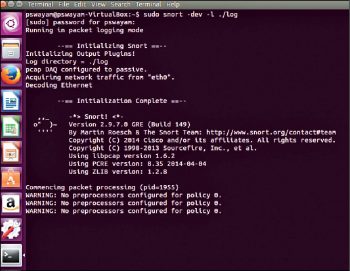
In packet logger mode, the main idea is to record the packets to the disk. In this mode, we need to specify a logging directory and Snort will automatically know how to get into the packet logger mode. A simple command to operate Snort in this mode looks like this:
pswayam@pswayam-VirtualBox:~$ snort –dev –l ./log
The above command assumes that you have a directory named log in the current directory. If that is not the case, Snort will exit with an error message. As expected, in order to log relative to the home network, you just need to tell Snort which the home network is. Another useful mode for logging is the binary mode and in this, Snort logs the packets in tcpdump format to a single binary file located in the logging directory. The following command shows how binary mode can be used:
pswayam@pswayam-VirtualBox:~$ snort –dev –l ./log –b
You can see from the above command that there is no need to specify the verbose mode or –d /-e switches. This is because, in binary mode, the entire packet is logged, not just parts of it.
If you need to enable network intrusion mode, you can use the following command:
pswayam@pswayam-VirtualBox:~$ snort –dev –l ./log -h $HOME_NET -c /etc/snort/ snort.conf
Please note that snort.conf is the name of your rule file and HOME_NET is a variable whose value is defined in the configuration file. The rule set defined in the snort.conf file will be applied to each packet, and a decision will be made on whether or not action needs to be taken. The default snort.conf references several other rule files, so it is a good idea to read through the entire snort.conf file before calling it from the command line.
It is also important to note here that if you are going to use Snort over a long period as an IDS, then do not use the –v switch in the command line for the sake of speed. When used as a network IDS, Snort provides near real-time intrusion detection capabilities.
Sometimes, you may be interested in the performance of Snort. In which case, you can use the –b and –A fast options. With these options, the packets will be logged in tcpdump format and you can expect very minimal alerts. The following command can be used for this purpose:
pswayam@pswayam-VirtualBox:~$ snort –b –A fast –c/etc/snort/snort.conf -lib
Snort applies its rules to packets in a specific order. The default order is that Alert rules will be applied first, then the Pass rules, and finally the Log rules. Snort provides a –o switch option to change the default rule application behaviour to Pass rules, then Alert, and then Log, as shown in the following command:
pswayam@pswayam-VirtualBox:~$ snort -d -h 192.168.1.0/24 -l ./log -c /etc/snort/snort.conf -o
Another important concept that we need to understand in Snort is output configurations. Snort provides a variety of options to display the output and the detected information. Please note that many Snort administrators use third-party applications to monitor and investigate the information generated by Snort. To do this, Snort must output the data in a particular format. One can enable multiple output plugins and these allow a variety of tools to be employed by Snort administrators. Let us have a quick look at some of these output configurations.
a. Alert syslog: UNIX based systems use the syslog facility to consolidate the generated messages. Snort-generated information can be presented to syslog in a number of ways. In this output configuration, the format looks like the following:
Output alert_syslog: <facility> <Priority>
An example is: output alert_syslog: LOG_AUTH LOG ALERT
b. Log tcpdump: This logs packets to the tcpdump file format. There are a variety of applications that can read this format.
c. MySQL: MySQL logging requires that the database support be present on the system running Snort, and that it is in the form of the MySQL client software and libraries.
After getting a clear understanding of Snort, a question will arise on where we need to place it. Putting Snort on each side of a firewall can be most enlightening. It is a best practice to run Snort behind a firewall, as this adds a layer of protection and is easier to manage.
Snort is considered the first choice when it comes to network IDS in many organisations. Cost-effectiveness and robustness are the two main parameters behind why people select it. But now with the several commercial versions of Snort available, industry support can be considered another reason behind its popularity. Added to this, the open source Snort community is also very active in providing the much needed support and enhancements of various features.













































































